Podcast
Questions and Answers
A computer is running slowly and frequently freezing. Which hardware component is the MOST likely culprit if other software issues have been ruled out?
A computer is running slowly and frequently freezing. Which hardware component is the MOST likely culprit if other software issues have been ruled out?
- Power Supply
- RAM (correct)
- Network Card
- Sound Card
When comparing SSDs and HDDs, which of the following is a key advantage of SSDs regarding data access?
When comparing SSDs and HDDs, which of the following is a key advantage of SSDs regarding data access?
- Lower cost per gigabyte
- Higher storage capacity for the same price
- Less susceptibility to data corruption
- Faster data access times (correct)
A user reports that their computer is unable to connect to the internet via a wired connection. After confirming the cable is properly connected, which hardware component is the MOST likely cause?
A user reports that their computer is unable to connect to the internet via a wired connection. After confirming the cable is properly connected, which hardware component is the MOST likely cause?
- Network Card (correct)
- Video Card (GPU)
- Power Supply
- Sound Card
Which operating system component is responsible for the abstraction of hardware interactions, allowing the rest of the OS and applications to interact with hardware in a consistent manner?
Which operating system component is responsible for the abstraction of hardware interactions, allowing the rest of the OS and applications to interact with hardware in a consistent manner?
An administrator needs to run multiple virtual machines on a single physical server. Which operating system capability is MOST crucial for achieving this?
An administrator needs to run multiple virtual machines on a single physical server. Which operating system capability is MOST crucial for achieving this?
Which of the following is the MOST direct function of the operating system kernel?
Which of the following is the MOST direct function of the operating system kernel?
A user needs to write a report. Which type of software application is MOST suitable for this task?
A user needs to write a report. Which type of software application is MOST suitable for this task?
A company needs to store customer data in a structured format for easy retrieval and analysis. Which type of software is MOST appropriate?
A company needs to store customer data in a structured format for easy retrieval and analysis. Which type of software is MOST appropriate?
A software developer is creating a new application. Which type of software provides a comprehensive set of tools for coding, debugging, and testing?
A software developer is creating a new application. Which type of software provides a comprehensive set of tools for coding, debugging, and testing?
A user receives an email claiming to be from their bank, requesting them to update their account information by clicking on a link. What type of online threat does this scenario MOST likely represent?
A user receives an email claiming to be from their bank, requesting them to update their account information by clicking on a link. What type of online threat does this scenario MOST likely represent?
A company wants to ensure that its employees' internet traffic is encrypted, especially when using public Wi-Fi networks. Which security measure is MOST effective for this purpose?
A company wants to ensure that its employees' internet traffic is encrypted, especially when using public Wi-Fi networks. Which security measure is MOST effective for this purpose?
A website displays 'HTTPS' in the address bar along with a padlock icon. What does this indicate about the website's security?
A website displays 'HTTPS' in the address bar along with a padlock icon. What does this indicate about the website's security?
A company wants to migrate its IT infrastructure to the cloud to reduce hardware costs and improve scalability. Which cloud computing model would provide the company with virtualized computing resources over the internet, allowing them to manage their own operating systems and applications?
A company wants to migrate its IT infrastructure to the cloud to reduce hardware costs and improve scalability. Which cloud computing model would provide the company with virtualized computing resources over the internet, allowing them to manage their own operating systems and applications?
A software company wants to provide its customers with access to its applications over the internet, without requiring them to install or manage the software on their own computers. Which cloud computing model is MOST suitable for this scenario?
A software company wants to provide its customers with access to its applications over the internet, without requiring them to install or manage the software on their own computers. Which cloud computing model is MOST suitable for this scenario?
An organization wants to leverage cloud computing while maintaining strict control over sensitive data. Which cloud deployment model is MOST appropriate?
An organization wants to leverage cloud computing while maintaining strict control over sensitive data. Which cloud deployment model is MOST appropriate?
What does the acronym CPU stand for?
What does the acronym CPU stand for?
Which of the following memory types is volatile, meaning it loses its data when power is removed?
Which of the following memory types is volatile, meaning it loses its data when power is removed?
Which of the following BEST describes the function of a GPU?
Which of the following BEST describes the function of a GPU?
Which of the following operating systems is open source?
Which of the following operating systems is open source?
Which type of Cloud Computing provides a platform for developing and deploying applications?
Which type of Cloud Computing provides a platform for developing and deploying applications?
Flashcards
Computer Hardware
Computer Hardware
Physical components of a computer system.
CPU (Central Processing Unit)
CPU (Central Processing Unit)
The primary component that executes instructions.
RAM (Random Access Memory)
RAM (Random Access Memory)
Computer's short-term memory for actively used data.
ROM (Read-Only Memory)
ROM (Read-Only Memory)
Signup and view all the flashcards
Motherboard
Motherboard
Signup and view all the flashcards
Storage Devices
Storage Devices
Signup and view all the flashcards
Input Devices
Input Devices
Signup and view all the flashcards
Output Devices
Output Devices
Signup and view all the flashcards
Operating System (OS)
Operating System (OS)
Signup and view all the flashcards
Kernel
Kernel
Signup and view all the flashcards
Device Drivers
Device Drivers
Signup and view all the flashcards
File Systems
File Systems
Signup and view all the flashcards
Software Applications
Software Applications
Signup and view all the flashcards
Word Processors
Word Processors
Signup and view all the flashcards
Web Browsers
Web Browsers
Signup and view all the flashcards
Internet Safety
Internet Safety
Signup and view all the flashcards
Malware
Malware
Signup and view all the flashcards
Cloud Computing
Cloud Computing
Signup and view all the flashcards
Software as a Service (SaaS)
Software as a Service (SaaS)
Signup and view all the flashcards
Cloud Storage
Cloud Storage
Signup and view all the flashcards
Study Notes
- Computer awareness encompasses understanding computer basics, hardware components, operating systems, software applications, internet usage, data security, and the impact of computers on society.
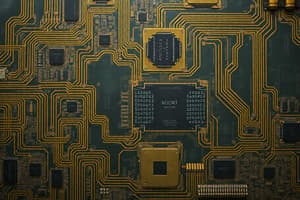
Basic Computer Hardware
- Computer hardware refers to the physical components of a computer system.
- The central processing unit (CPU) is the primary component that executes instructions.
- CPU speed is measured in gigahertz (GHz), representing the number of instructions it can process per second.
- Random access memory (RAM) is the computer's short-term memory, used for temporarily storing data and instructions that the CPU is actively using.
- Read-only memory (ROM) stores firmware and critical system instructions that are retained when the computer is powered off.
- The motherboard is the main circuit board that connects all computer components.
- Storage devices include hard disk drives (HDDs) and solid-state drives (SSDs), which store data persistently.
- HDDs use magnetic platters to store data, while SSDs use flash memory for faster data access and greater durability.
- Input devices allow users to enter data into the computer (e.g., keyboard, mouse, scanner).
- Output devices display or present data from the computer (e.g., monitor, printer, speakers).
- Video cards (GPUs) process and output images to the monitor.
- Sound cards process audio signals for speakers and microphones.
- Network cards enable the computer to connect to a network.
- Power supplies provide electricity to all components.
Operating Systems
- An operating system (OS) manages computer hardware and software resources.
- The OS provides a platform for software applications to run.
- Popular desktop operating systems include Windows, macOS, and Linux.
- Mobile operating systems include Android and iOS.
- The kernel is the core of the OS, responsible for managing the system's resources.
- Device drivers enable the OS to communicate with hardware devices.
- File systems organize and manage files and directories on storage devices.
- User interfaces (UIs) allow users to interact with the OS, including graphical user interfaces (GUIs) and command-line interfaces (CLIs).
- Multitasking allows the OS to run multiple programs simultaneously.
- Memory management involves allocating and deallocating memory to programs.
- Process management involves managing the execution of programs.
- Security features protect the system from unauthorized access and malware.
Software Applications
- Software applications are programs designed to perform specific tasks.
- Word processors (e.g., Microsoft Word, Google Docs) are used for creating and editing documents.
- Spreadsheets (e.g., Microsoft Excel, Google Sheets) are used for organizing and analyzing data.
- Presentation software (e.g., Microsoft PowerPoint, Google Slides) is used for creating and delivering presentations.
- Database management systems (DBMS) (e.g., MySQL, Oracle) are used for storing and managing structured data.
- Web browsers (e.g., Chrome, Firefox, Safari) are used for accessing the internet.
- Email clients (e.g., Outlook, Gmail) are used for sending and receiving emails.
- Graphics editors (e.g., Adobe Photoshop, GIMP) are used for creating and editing images.
- Video editing software (e.g., Adobe Premiere Pro, iMovie) is used for creating and editing videos.
- Integrated development environments (IDEs) (e.g., Visual Studio, Eclipse) provide tools for software development.
- Anti-virus software protects computers from malware.
- Software suites (e.g., Microsoft Office, Adobe Creative Suite) bundle multiple applications together.
Internet Safety
- Internet safety involves protecting oneself from online threats and risks.
- Malware includes viruses, worms, and Trojan horses that can harm or compromise computer systems.
- Phishing is a form of online fraud where attackers try to trick users into revealing personal information.
- Strong passwords should be used to protect online accounts.
- Firewalls can prevent unauthorized access to computer networks.
- Virtual private networks (VPNs) encrypt internet traffic to protect privacy.
- Secure websites use HTTPS encryption to protect data transmitted between the user and the website.
- Social engineering involves manipulating people into divulging confidential information.
- Regular software updates patch security vulnerabilities.
- Public Wi-Fi networks may not be secure and can expose data to interception.
- Online scams can involve fake products, services, or investment opportunities.
- Cyberbullying involves using electronic communication to harass or intimidate someone.
- Identity theft involves stealing someone's personal information to commit fraud.
Cloud Computing
- Cloud computing involves delivering computing services over the internet.
- Infrastructure as a Service (IaaS) provides virtualized computing resources over the internet.
- Platform as a Service (PaaS) provides a platform for developing and deploying applications.
- Software as a Service (SaaS) provides software applications over the internet.
- Public clouds are owned and operated by third-party providers.
- Private clouds are owned and operated by an organization for its own use.
- Hybrid clouds combine public and private cloud resources.
- Cloud storage allows users to store data remotely on servers accessible over the internet.
- Cloud computing can offer scalability, flexibility, and cost savings.
- Cloud security involves protecting data and applications stored in the cloud.
- Virtualization is a key technology that enables cloud computing by creating virtual versions of hardware and software resources.
Studying That Suits You
Use AI to generate personalized quizzes and flashcards to suit your learning preferences.