Podcast
Questions and Answers
What is the main purpose of a Trojan horse malware?
What is the main purpose of a Trojan horse malware?
- To deceive users into downloading and installing it (correct)
- To enhance the performance of antivirus software
- To provide authorized access to a system
- To perform regular system updates
How can users prevent Trojan horse attacks?
How can users prevent Trojan horse attacks?
- Update software and operating systems regularly (correct)
- Click on links from unknown sources
- Disable antivirus software
- Install all available software without checking the source
Which of the following is NOT a potential activity of Trojan horse malware?
Which of the following is NOT a potential activity of Trojan horse malware?
- Enhancing system performance (correct)
- Providing unauthorized access to the compromised system
- Stealing sensitive information
- Installing other malware
Why is it important to be cautious when downloading software from unknown sources?
Why is it important to be cautious when downloading software from unknown sources?
What common theme do the Trojan horse myth from Greek mythology and the modern-day cybersecurity term share?
What common theme do the Trojan horse myth from Greek mythology and the modern-day cybersecurity term share?
Which action is NOT recommended for protecting against Trojan horse attacks?
Which action is NOT recommended for protecting against Trojan horse attacks?
What is the modern-day usage of the term 'Trojan horse' in the context of cybersecurity?
What is the modern-day usage of the term 'Trojan horse' in the context of cybersecurity?
Who was Helen of Troy in the context of the Trojan War?
Who was Helen of Troy in the context of the Trojan War?
What sparked the Trojan War?
What sparked the Trojan War?
How did the Trojan War end?
How did the Trojan War end?
In the context of cybersecurity, what is the significance of a 'Trojan horse' as a metaphor?
In the context of cybersecurity, what is the significance of a 'Trojan horse' as a metaphor?
What was the purpose of the wooden horse in the Trojan War?
What was the purpose of the wooden horse in the Trojan War?
Flashcards are hidden until you start studying
Study Notes
The Trojan Horse: A Greek Myth and a Cybersecurity Term
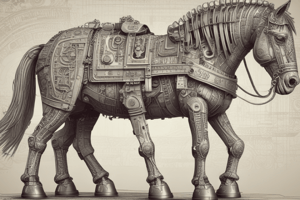
The term "Trojan horse" is often used in the context of cybersecurity, referring to a malicious program that is disguised as a harmless one, allowing unauthorized access to a computer system or network. This term originates from the ancient Greek myth of the Trojan War, which provides an interesting historical backdrop to the modern-day usage.
The Trojan War
The Trojan War was a legendary ten-year siege of the city of Troy by the Greek king Agamemnon and his allies. The war was fought over Helen of Troy, who was abducted by Paris, a prince of Troy, sparking a series of events that led to the conflict. The Greeks built a large wooden horse, in which they hid soldiers and left it as a 'gift' for the Trojans. The Trojans, believing they had won the war, pulled the wooden horse inside their walls, and the Greek soldiers emerged, sacked the city, and ended the war.
The Wooden Horse
The wooden horse was the deceptive gift that the Greeks used to infiltrate the city of Troy. It served as a metaphor for the concept of a Trojan horse in modern cybersecurity. A Trojan horse is a type of malware that is disguised as a legitimate program. When a user downloads and installs the Trojan, it infiltrates their computer, providing unauthorized access to the system. This can lead to data theft, identity theft, or other malicious activities.
The Cybersecurity Connection
In the context of cybersecurity, the term "Trojan horse" refers to a type of malware that is designed to trick users into downloading and installing it. Once installed, the malware can perform various malicious activities, including stealing sensitive information, installing other malware, or providing unauthorized access to the compromised system.
Prevention and Mitigation
To prevent or mitigate Trojan horse attacks, it is essential to maintain up-to-date antivirus software and regularly scan your computer for malware. Be cautious when downloading software or clicking on links from unknown sources, as these can often be hiding a hidden threat. It is also crucial to keep all software and operating systems updated, as these updates often include security patches.
In conclusion, the Trojan horse myth from Greek mythology and the modern-day cybersecurity term share a common theme of deception and infiltration. Understanding the historical context and the modern-day implications of the term can help users better protect themselves from potential threats.
Studying That Suits You
Use AI to generate personalized quizzes and flashcards to suit your learning preferences.